Southern Computer Services SA provides a mobile computer repair service in Adelaide's Southern & Western suburbs. We are 100% South Australian-owned & operated.
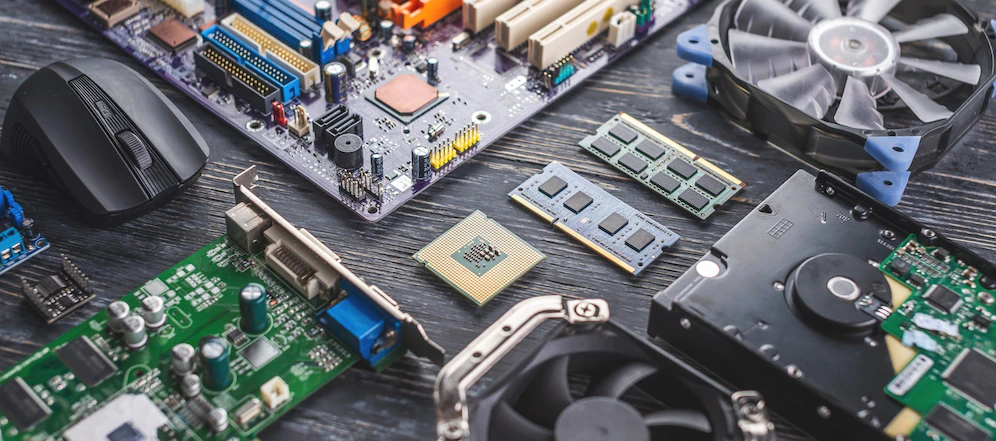
We can help with all home computer repairs & servicing, including Laptop & Desktop PC Repairs, NBN Internet issues, Windows 10 Upgrades, Malware, Virus, Adware and Spyware Removal, as well as Email help & support.
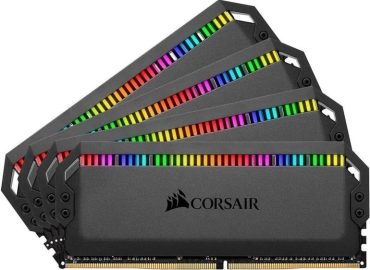
Additionally, we can upgrade your slow Hard Drive to a
super-fast Solid State Drive (SSD). Our services include on-site Computer Setup, Data Recovery and Data Backup. Our experienced computer technicians can also provide technical help & support with Wifi modem, Bluetooth and printer issues.
As we are a purely mobile repair service we don't have the high overheads of maintaining a computer repair shop, so we can pass these savings on to YOU. Please ask us for a quote on a new custom Desktop Computer build!
FREE Call-Out and No Hidden Charges
You only pay for the time taken to fix your PC, which is fixed at an extremely competitive $129 for the first hour on site (maximum 2 hour charge). There is NO additional 'callout' fee.
We also have fixed rates for some common services. For example a Windows reinstall is just $149 which includes a full format of your hard drive, a fresh install of Windows & all updates. Additionally, we install Google Chrome, Adobe Reader and other essential 3rd party software which doesn't come standard with Windows 10/11. Also included in the price is FREE pickup and return of your computer (subject to our coverage area).
For just $89 we can also provide you with a written insurance repair quote for accidental damage outlining the cost of repairs for your insurer. This fee is then generally reimbursed to you by most insurers.
Our payment facilities include cash, bank transfer and credit or debit card payments and we are also open on weekends & public holidays.